POET is a three-day cyber foundational course designed for cleared industry personnel, military members, and government civilians tasked with supporting control systems, embedded assets, and critical infrastructure. It establishes a functional baseline for reverse engineering within the Cyber-Physical Systems (CPS) domain, providing the technical framework necessary for further specialization.
Guided by our expert instructors, participants will gain hands-on experience identifying, disassembling, and interpreting software binaries using industry-standard tools like Ghidra. The curriculum moves beyond the OS level to analyze the physical layer, examining electronic components, firmware architectures, and the communication interfaces that link embedded peripherals within a CPS environment. Finally, you will use diagnostic instruments to observe and verify real-time electronic behavior.
Born out of necessity after dissatisfaction with available cyber training, POET delivers operator-in-the-loop training, advisory, and consulting support in technology, engineering, and cybersecurity, designed by defense experts and entrepreneurs in defense tech. This course is purpose-built to uplift current defense training with modules that build foundational understanding of technology design at the OS level.
Participants receive a formal course certificate supporting DoW and DIB qualification pathways upon completion.
The POET curriculum is structured as a progressive ladder, where each level removes specific failure modes and prepares analysts for increasingly advanced offensive operations.
Basic embedded familiarity, tooling exposure, and firmware awareness
Evidence handling, ambiguity tolerance, and toll control that prevent exploitation failure
Flash extraction, execution reconstruction, and architecture-driven exploitation
Each level is intentionally incomplete on its own. Capability emerges from progression, not from skipping levels.

Defense contractors

DIB technical SMEs

OT and control systems engineers

Military and governmet cyber personnel

Cybersecurity professionals expanding into ICS/SCADA exploitation
Designed for technical practitioners with foundational knowledge in:

Cybersecurity

Network engineering

Operational technology
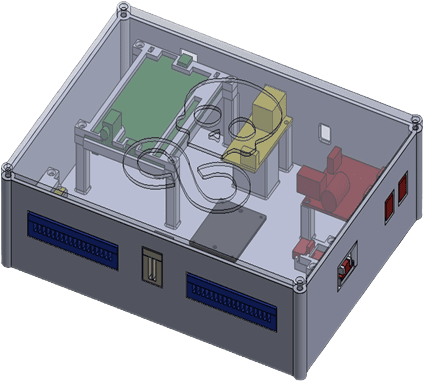
 Core Embedded Testbed Unit
Core Embedded Testbed Unit Patch Panel Interface
Patch Panel Interface Wiring Harness Kit
Wiring Harness Kit I2C EEPROM Expansion Module
I2C EEPROM Expansion Module SPI Flash Expansion Module
SPI Flash Expansion Module Developer Quick Start Guide
Developer Quick Start Guide
Infinity Labs LLC delivers both advanced technical solutions and business-focused advisory services across cyber and operational domains.
Technical & Engineering Services

Cyber technology development for ICS/SCADA environments

Cyber testbed design, development, and integration

Modeling, simulation, and cyber experimentation platforms

Applied cybersecurity engineering and analysis
Business & Advisory Services

Cybersecurity strategy development for operational environments

Business consulting on cyber program implementation and risk management

Operational planning and program support for cyber initiatives

Advisory services for integrating cyber capabilities into business and mission operations